The Reasons You Should Integrate IAM With Data Center Security | Unleash Your Productivity – Unleash Blog

Integrate AWS IAM Identity Center (successor to AWS Single Sign-On) with AWS Lake Formation fine-grained access controls - Global Intelligence and Insight Platform: IT Innovation, ETF Investment

The Reasons You Should Integrate IAM With Data Center Security | Unleash Your Productivity – Unleash Blog
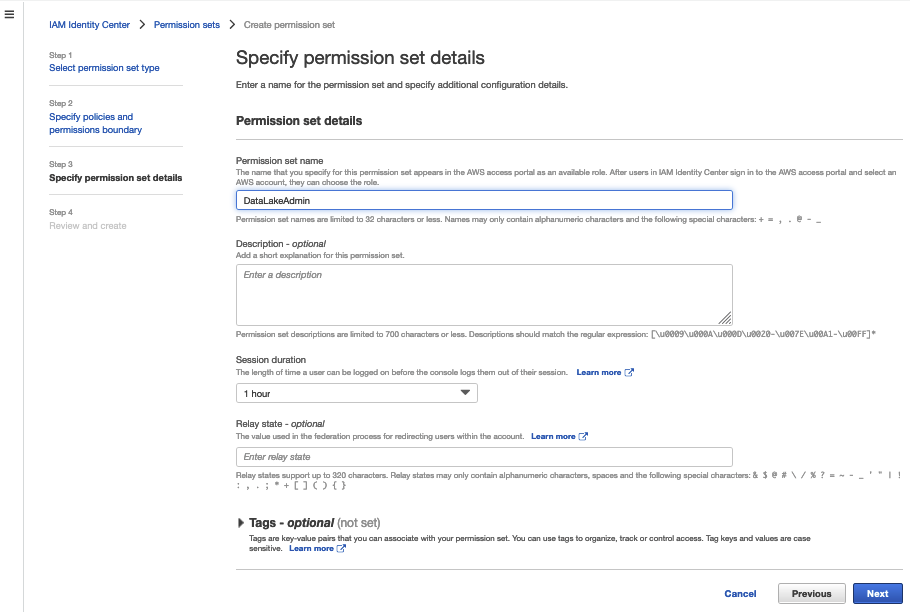
Integrate AWS IAM Identity Center (successor to AWS Single Sign-On) with AWS Lake Formation fine-grained access controls | AWS Big Data Blog

The Reasons You Should Integrate IAM With Data Center Security | Unleash Your Productivity – Unleash Blog

Integrate AWS IAM Identity Center (successor to AWS Single Sign-On) with AWS Lake Formation fine-grained access controls - Global Intelligence and Insight Platform: IT Innovation, ETF Investment

Integrate AWS IAM Identity Center (successor to AWS Single Sign-On) with AWS Lake Formation fine-grained access controls - Global Intelligence and Insight Platform: IT Innovation, ETF Investment

Integrate AWS IAM Identity Center (successor to AWS Single Sign-On) with AWS Lake Formation fine-grained access controls | AWS Big Data Blog